OWASP Top 10 Pentesting with Penti: Vulnerable and Outdated Components
Don’t risk exposure to vulnerabilities hidden within the third-party tools that you rely on. Launching Penti enables continuous testing of your applications for vulnerable and outdated components using real‑world attack simulation, AI‑driven validation, and expert oversight. Penti’s agents rapidly surface the exploitable weaknesses hiding in your tech stack.
Vulnerable and Outdated Components: Overview
Human-Verified Findings Prioritized by Business Impact
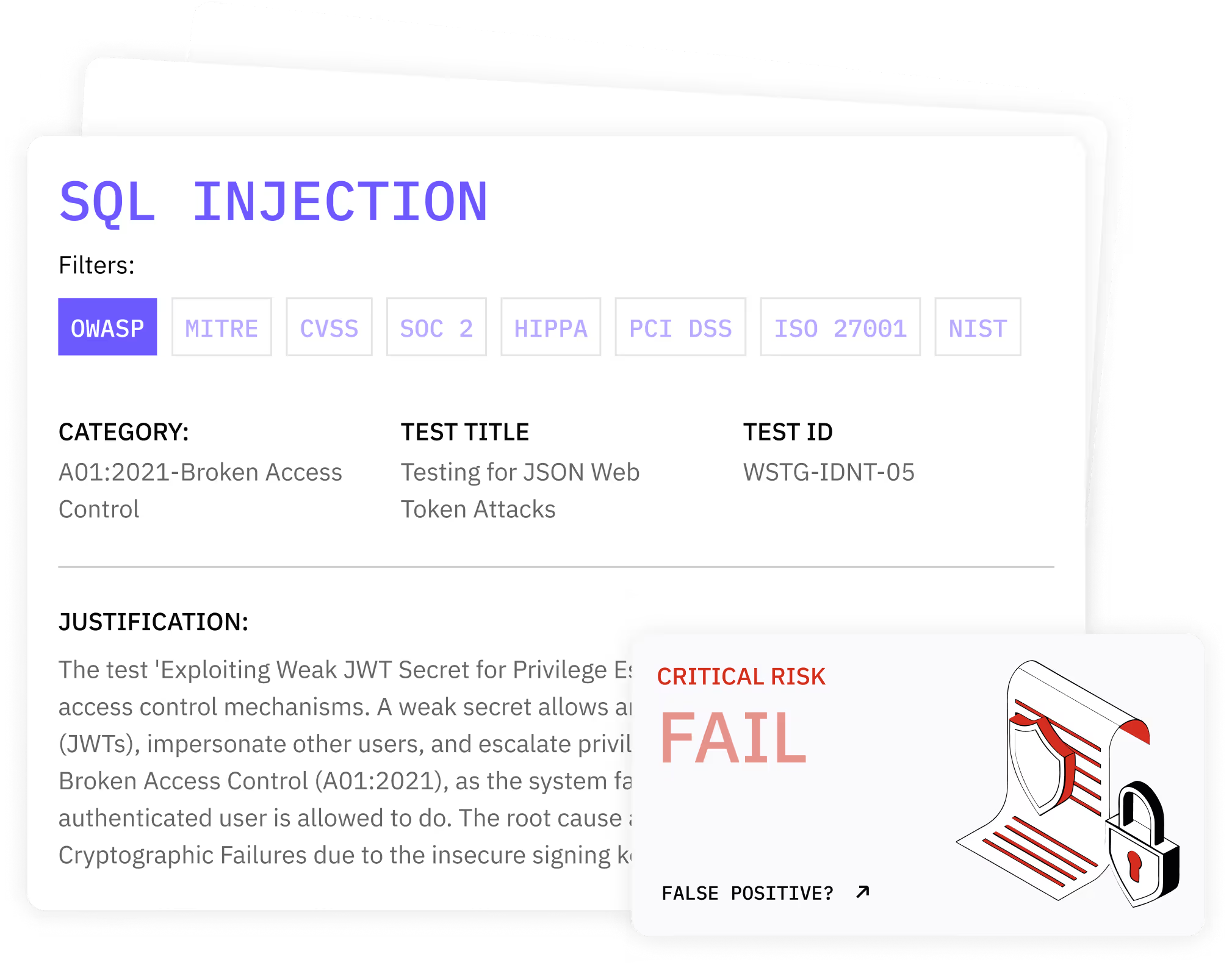
Penti’s agents rapidly scan your attack surface for vulnerabilities, then simulate real world attacks, challenging your security defenses and providing a prioritized roadmap for remediation, so that you’re not wasting time parsing through endless outputs from automated scanners.
Simulated attacker behavior against third party components
Clear proof of impact tied to application functionality

Reduced false positives compared to inventory‑only checks
Actionable remediation guidance aligned with development workflows
How Penti Detects Vulnerable and Outdated Components
Penti initially maps application behavior and identifies software components in use across your environment. This includes direct code usage and indirect relationships such as transitive dependencies introduced through packages and frameworks. Our pentesters analyze discovered versions against known vulnerabilities and public disclosures.Next, Penti moves beyond identification. Agentic AI simulates exploitation paths that attackers use to exploit vulnerabilities. Each potential weakness is tested safely within controlled boundaries to determine whether it can be abused in your organization’s deployment process and runtime configuration.
Penti validates whether outdated version usage can trigger security flaws under real conditions. This includes testing access paths, privilege boundaries, and exposure of sensitive information. Findings are confirmed only when Penti can demonstrate realistic impact instead of theoretical risk and after human experts have reviewed the results. Unlike other automated tools, Penti eliminates noise and highlights exploitable vulnerabilities that require immediate attention.
Key features
- Discovery of vulnerable and outdated components across application layers
- Correlation with security advisories and known issues
- Context‑aware testing instead of inventory‑only reporting
- Safe exploitation attempts to confirm real impact
- Continuous testing as code and libraries change
- Support for common ecosystems and software frameworks
What clients receive
- A verified list of exploitable findings with reproduction steps
- Clear evidence showing how vulnerabilities can be abused
- Risk‑based prioritization aligned to business impact
- Guidance for remediation and future security checks
How Penti helps you reduce risks from outdated software
Penti helps teams go from detection to reducing security exposure in the long-term. Each finding includes guidance on security updates, upgrade paths, and compensating controls, empowering teams to remediate faster without slowing delivery.
Penti integrates with development workflows, supporting better version management and stronger patch management across environments. Penti’s unlimited and continuous testing ensures that fixes remain effective as new packages and libraries are introduced.
.svg)
.svg)
.svg)
.avif)

Trusted by Security Teams that Need Evidence
Security leaders rely on Penti to uncover risks that traditional tools miss. Our user-friendly dashboard delivers prioritized findings, audit-ready documentation and expert-validated remediation roadmaps.
FAQ
What is a vulnerable component?
A vulnerable component is any external code or service that contains known weaknesses. Malicious actors can manipulate these weaknesses to bypass controls, access data, or disrupt systems. Components typically become vulnerable when flaws are disclosed publicly and remain unpatched.
What does “outdated” mean in security terms?
Outdated components are running an older version that no longer receives fixes or support. These no longer supported versions can contain known security vulnerabilities that attackers take advantage of.
How do organizations know which components are vulnerable?
Organizations typically rely on vulnerability testing and correlation with public databases. Penti enhances this by validating whether identified weaknesses are actually exploitable in your environment instead of relying on lists alone.
Why are third‑party components so risky?
Third party components are widely reused and well studied by attackers. When a flaw is disclosed, it becomes a common attack vector across many applications. Without strong software dependencies management, these risks accumulate quietly.
How does this help prevent breaches?
By identifying exploitable weaknesses early, teams can apply fixes before attackers act. This reduces exposure to common vulnerabilities, protects sensitive information, and lowers the likelihood of costly incidents tied to outdated software.














