OWASP Top 10 Pentesting with Penti: Security Logging and Monitoring Failures
Security Logging and Monitoring Failures are among the most prevalent threats facing fast-growing companies regardless of industry. When attackers exploit these gaps in visibility, they can travel through your systems without being detected right away. Penti’s agentic platform uncovers blind spots by validating whether your applications reliably record and surface critical security signals.
Security Logging and Monitoring Failures: Overview
Why Test Logging and Monitoring Controls with Penti
Penti’s approach to testing for Security Logging and Monitoring Failures focuses on validating visibility, traceability, and response readiness across your environment.
Verify real‑world coverage

Detect blind spots early
Improve response readiness

Support compliance and risk reduction
How Penti’s Agents Target and Validate Logging and Monitoring Failures
Penti performs adversarial testing designed to confirm whether security relevant events are captured and surfaced when attackers attempt to gain unauthorized access or abuse legitimate functionality. AI agents simulate behavior that should trigger records such as failed logins. The system then validates whether these events appear in log files and alerting systems.
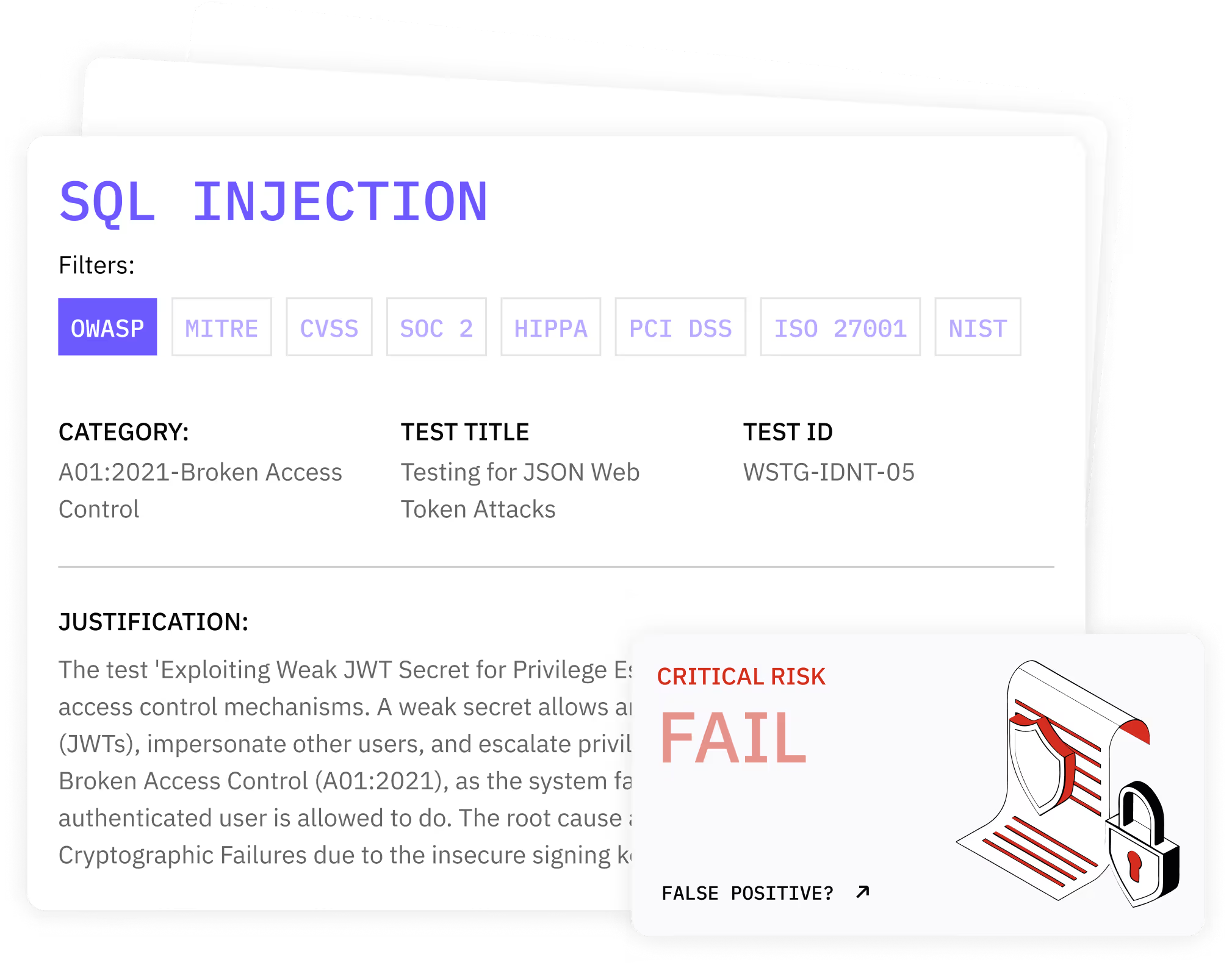
Key features
- Simulates login attempts from the same IP address and varied sources to verify logging failed login attempts
- Tests whether critical security events are captured during privilege abuse and access controls bypass attempts
- Evaluates centralized monitoring and real-time monitoring coverage during attack simulation
- Identifies inadequate logging tied to system configurations and application logic
- Assesses log integrity to ensure records cannot be altered or silently dropped
- Validates whether automated tools receive sufficient signals without creating alert fatigue
What clients receive
- A verified list of Security Logging and Monitoring Failures with reproduction steps
- Evidence showing whether applications properly record attempted abuse paths
- Clear guidance on improving adequate logging and monitoring practices
- Compliance‑ready artifacts supporting audit and remediation cycles
How Penti Helps Teams Prepare for Modern Threats
.svg)
.svg)
.svg)
.avif)

Trusted by security‑conscious teams
Teams trust Penti because findings reflect real attack behavior rather than hypothetical weaknesses. Our agentic platform produces client-ready reports on core concerns that surface during incidents involving malicious activities and potential threats.
FAQ
What are Security Logging and Monitoring Failures?
Security Logging and Monitoring Failures occur when systems do not reliably log security events or fail to surface them to defenders. This includes missing records for authentication abuse, lack of alerts for anomalous behavior, or logs that cannot support investigation after security incidents.
Why do attackers target logging weaknesses?
Attackers rely on stealth. When monitoring systems fail to detect or alert on abuse, adversaries can move laterally, access sensitive information, and persist for long periods. Weak logging gives them confidence that their actions will go unnoticed.
How does pentesting differ from log configuration reviews?
Configuration reviews assess whether logging is enabled. Pentesting validates whether logs are actually produced during real attack scenarios. Penti confirms whether important security events appear where defenders expect them during attacks.
What systems does Penti test?
Penti focuses on web applications and supporting services where monitoring failures organizations commonly overlook. This includes authentication flows, data access paths, and business logic where attackers often hide.
Can this testing help with incident response preparation?
Yes. By validating what gets recorded and surfaced, teams know whether they can rely on existing signals during incident response. This reduces delays during investigations and supports faster containment.
How often should logging and monitoring be tested?
Logging should be tested regularly as applications change. New features can introduce gaps that prevent security logging and monitoring from functioning as expected. Continuous testing helps ensure coverage remains intact.














