OWASP Top 10 Pentesting with Penti: Cryptographic Failures
OWASP Top 10 Cryptographic Failures are security vulnerabilities that can pose serious risks to your systems by exposing sensitive data to malicious actors. Penti’s platform offers human-verified agentic testing for cryptographic failures, backed by curated threat intelligence. We deliver client-ready evidence reports that prove your organization has all necessary safeguards in place to protect encrypted data.
Cryptographic Failures: Overview
Protect Sensitive Data with Penti’s Security Testing for Cryptographic Failures
Early Detection of Real-World Cryptographic Risks
Verified Visibility Into Key and Token Exposure

Clear Business Impact and Prioritized Fixes
Audit‑Ready Evidence and Developer‑Friendly Guidance

How Penti Detects and Validates Cryptographic Failures
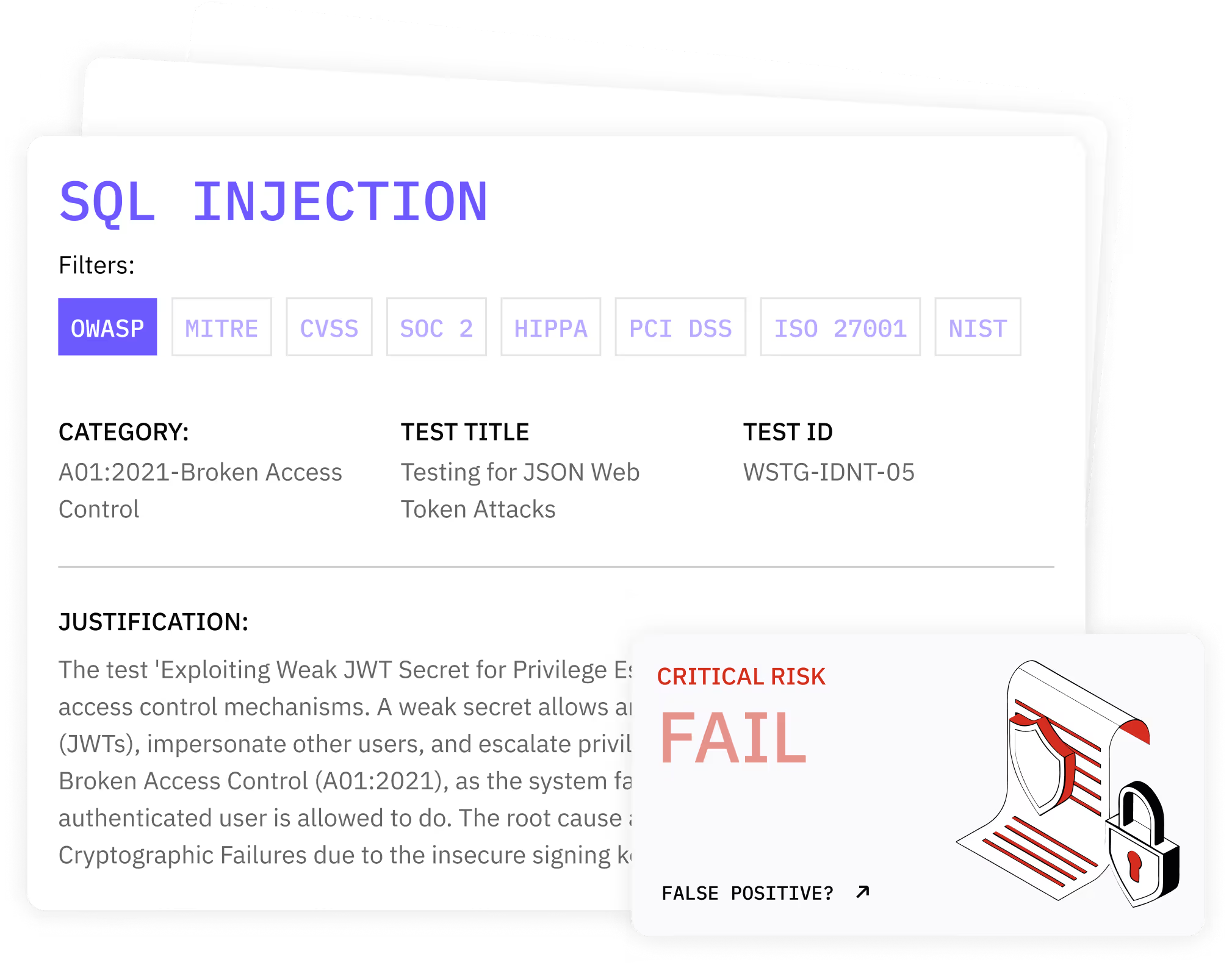
Key features
- Protocol and cipher review that detects weak cipher suites and legacy protocols.
- TLS hardening checks that verify strict transport security and http strict transport security.
- Algorithm analysis that flags broken cryptographic algorithms and outdated encryption algorithms.
- Entropy and randomness tests that catch insufficient entropy and insecure random number generation.
- Crypto misuse detection that inspects initialization vectors, key generation, and storing keys securely.
- Workflow tracing that shows where apps encrypt sensitive data and where secure communication protocols fall short.
What clients receive
- Reproducible proof of issues with step-by-step evidence.
- Impact analysis that shows what an attacker could access or decrypt sensitive information.
- Developer-ready guidance for proper key management and safe library upgrades.
- A retest plan that confirms fixes and locks in secure encryption algorithms and strong encryption algorithms.
Results: Detect, Fix, and Reduce Risk
.svg)
.svg)
.svg)
.avif)

Trusted by Engineering Teams Who Put Security First
Risk owners and engineering leaders integrate Penti to uncover hidden cryptographic issues and close them fast. Our clients value verified results, reduced false positives, and straightforward guidance that turns complex crypto risks into simple, high-impact solutions.
FAQ
What are cryptographic problems?
Cryptographic problems are defects in cryptographic algorithms, implementations, or protocol use that weaken protection. Common problems include weak configurations, outdated algorithms, and misuse of libraries. These issues can expose sensitive information and lead to data exposure or identity theft.
How do you avoid the risk of cryptographic failures?
Adopt cryptographic best practices and secure coding practices. Use strong encryption algorithms and secure communication protocols. It’s crucial to enforce proper key management with rotation and revocation and keep your libraries current. Don’t forget to test often to prevent cryptographic failures before release.
What does Penti test for in cryptography?
Penti inspects cipher and protocol choices for weak cipher suites and legacy protocols. Our agents check for broken cryptographic algorithms and outdated algorithms and validate entropy sources to catch insufficient entropy and padding oracle attacks. Penti examines initialization vectors, key generation, and how apps handle storing keys securely and encryption keys.
Will testing disrupt production?
No. Penti uses safe probes and guardrails. Agents validate risks without service interruption. You control scope and timing. You can run in non-production for deeper checks. Findings always include impact and reproduction steps.
What evidence do we receive for audits?
You receive client-ready reports with proof of exploit, business impact, and remediation steps. Evidence maps to policies and controls. It supports reviews that require cryptographic controls and data protection verification.
How does this testing reduce business risk?
Penti’s platform helps your team close gaps that let attackers exploit cryptographic flaws and access sensitive data. Our fixes protect financial data and other regulated records. You strengthen trust with customers and partners while improving time to compliance.














