OWASP Top 10 Pentesting with Penti: Software and Data Integrity Failures
Penti pinpoints OWASP Top 10 Risks like Software and Data Integrity Failures and offers tailored remediation steps that security teams can act on immediately and safeguard customer confidence. Don’t let unvalidated code, updates, and pipelines leave your systems exposed.
Software and Data Integrity Failures: overview
Confirm Exploitable Weaknesses and Prevent Attacks
Companies that rely on complex software ecosystems that include plugins, repositories, and third‑party dependencies face complicated risks. A single weakness can expose critical data and introduce lasting weaknesses. Penti’s autonomous agents dig into your web application’s code and data integrity, providing clarity into the impacts of these vulnerabilities.
Business‑relevant findings

In-depth testing of modern delivery models
Scalable security assessments

Stronger governance and trust
How Penti Zeroes-in on Security and Data Integrity Failures
Penti’s OWASP Top 10 testing combines autonomous AI agents with expert oversight to analyze how your applications handle software and data throughout their lifecycle. Our platform evaluates trust boundaries across build, distribution, and runtime environments to identify where untrusted sources can influence execution or stored information.
Key features
- Analyzes software supply chain flows including software updates and external libraries
- Safely attempts to inject malicious code through controlled test paths
- Evaluates validation of digital signatures and checksum handling
- Tests handling of untrusted data entering application logic or storage
- Identifies vulnerable components that are no longer supported or patched
- Correlates findings with known vulnerabilities to confirm real exposure
What clients receive
- A verified list of Software and Data Integrity Failures with clear reproduction steps
- Technical proof that demonstrates how attackers could inject malicious data
- Prioritized remediation guidance aligned to business impact
- Retest recommendations to confirm fixes remain effective over time
How Penti helps teams fix and reduce integrity risk
.svg)
.svg)
.svg)
.avif)

Trusted by security and engineering teams
Organizations choose Penti because it delivers prioritized findings, not just alerts. Organizations of all sizes turn to Penti to surface real risk, validate impact, and explain findings in a way that aligns security teams and business stakeholders around remediation priorities.
Explore Related OWASP Authentication & Security Risks
Authentication weaknesses often intersect with insecure access controls, misconfigurations, and vulnerable components. Explore related OWASP pentesting categories to uncover additional attack paths before attackers do.
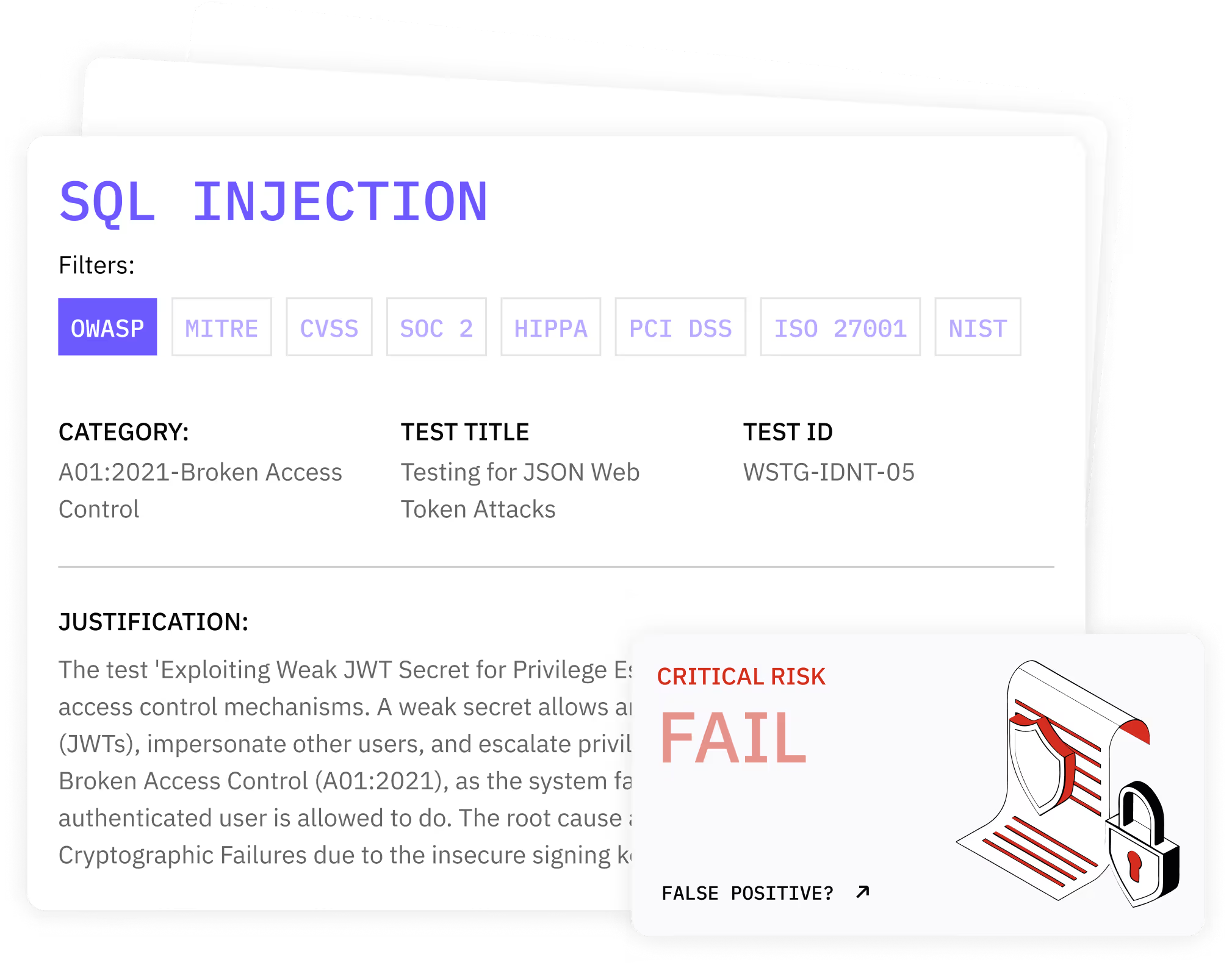
SQL Injection
Server-Side Request Forgery
Security Misconfiguration
Broken Access Control
Cryptographic Failures
Insecure Design
Identification and Authentication Failures
Vulnerable and Outdated Components
FAQ
What are Software and Data Integrity Failures?
Software and Data Integrity Failures happen when applications fail to verify the authenticity or integrity of software, updates, or data. Attackers exploit this to introduce malware, alter application behavior, or corrupt business processes without triggering immediate detection.
Why are integrity failures difficult to detect?
Unlike visible application errors, integrity problems often occur behind the scenes during downloads, updates, or data exchanges. Without proper validation, unauthorized changes blend into normal operations and remain unnoticed until damage occurs.
What types of systems does Penti test for integrity issues?
Penti evaluates web applications, APIs, CI/CD pipelines, and deployment environments. Testing includes how applications handle configuration files, update packages, and externally sourced components.
How does this help prevent future attacks?
Validated findings allow teams to fix root causes rather than symptoms. Strengthening verification processes helps prevent attackers from crossing trust boundaries or introducing unauthorized logic in the future.
Will testing disrupt our production environment?
No. Penti performs testing in a controlled manner designed to avoid service interruption while still confirming real exploit paths and failure conditions.
How often should organizations test for integrity failures?
Testing should occur regularly, especially after architectural changes, new releases, or dependency updates. Continuous validation helps organizations minimize exposure as their software evolves.














